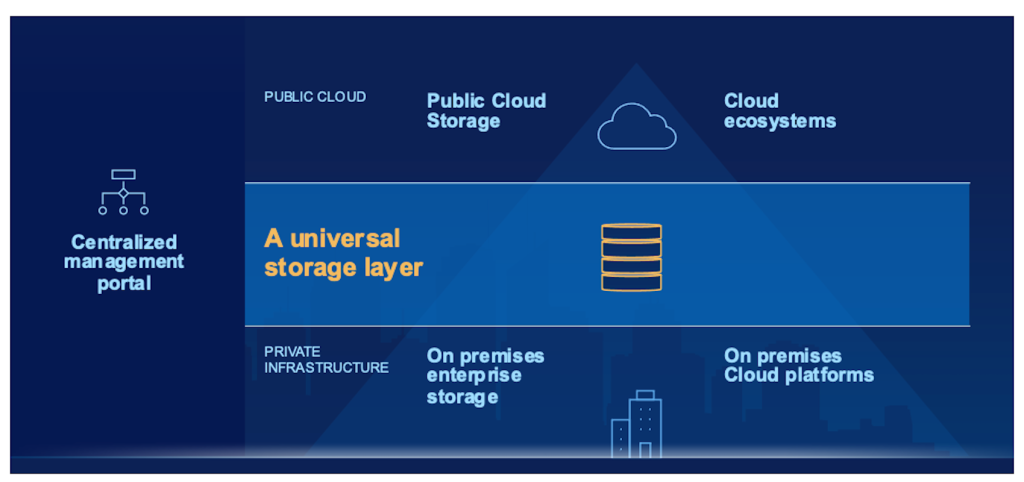
Checking Out the Function of Universal Cloud Storage Space Solutions in Data Defense and Compliance
As businesses significantly depend on cloud storage space remedies to manage and secure their data, discovering the detailed duty these services play in ensuring data protection and conference regulative criteria is important. By diving right into the nuances of universal cloud storage solutions, a more clear understanding of their influence on data safety and regulative compliance arises, shedding light on the intricacies and chances that lie ahead.
Significance of Cloud Storage Space Solutions
Cloud storage space services play an essential role in contemporary data administration techniques due to their scalability, accessibility, and cost-effectiveness. Scalability is a crucial benefit of cloud storage, allowing companies to easily readjust their storage space ability as data needs rise and fall.
Access is an additional important element of cloud storage solutions. By saving data in the cloud, users can access their information from anywhere with a web link, facilitating partnership and remote work. This access advertises operational efficiency and allows smooth sharing of information throughout teams and locations.
In addition, numerous cloud storage space suppliers offer pay-as-you-go prices designs, permitting organizations to pay only for the storage ability they make use of. On the whole, the value of cloud storage solutions exists in their ability to enhance information management procedures, improve ease of access, and reduced operational prices.
Information Security Approaches With Cloud
Carrying out durable data encryption protocols is vital for making certain the safety and discretion of information stored in cloud settings. Encryption plays a critical function in protecting data both in transit and at rest. By securing data before it is uploaded to the cloud and preserving control over the file encryption keys, organizations can protect against unauthorized accessibility and minimize the risk of data violations. In addition, implementing gain access to controls and authentication systems aids in controlling that can access the data kept in the cloud. Multi-factor verification, solid password policies, and normal access reviews are some strategies that can improve information defense in cloud storage services.
On a regular basis supporting information is one more essential element of data security in the cloud. By producing backups saved in separate places, organizations can make certain information accessibility and resilience in case of unexpected events such as cyber-attacks, hardware failures, or all-natural catastrophes. Additionally, performing routine security audits and assessments can help determine susceptabilities and guarantee compliance with information security guidelines. By combining file encryption, access controls, back-ups, and routine safety analyses, organizations can establish a durable information defense technique in cloud atmospheres.
Compliance Factors To Consider in Cloud Storage
Offered the vital nature of information security techniques in cloud environments, organizations should also prioritize conformity factors to consider when it pertains to keeping data in the cloud. Conformity demands differ across sectors and areas, making it essential for companies to recognize and stick to the pertinent policies. When using cloud storage space solutions, services require to guarantee that the copyright adheres to industry-specific standards such as GDPR, HIPAA, or PCI DSS, relying on Web Site the sort of data being stored. Furthermore, organizations have to consider information residency needs to ensure that information is stored in certified areas.
Challenges and Solutions in Cloud Protection
Guaranteeing durable safety and security steps in cloud environments offers a diverse challenge for organizations today. Among the main challenges in cloud protection is data breaches. Harmful stars continuously target cloud systems to gain unapproved access to sensitive details. To reduce this danger, companies need to implement strong file encryption methods, access controls, and normal safety audits. Another obstacle is the common duty design in cloud computing, where both the cloud company and the consumer are accountable for different aspects of safety and security. This can lead to complication and voids in safety coverage if not plainly defined. Organizations has to plainly outline roles and duties to ensure extensive protection steps are in area.
Future Patterns in Cloud Information Security
The advancing landscape of cloud information security is marked by a growing emphasis on aggressive defense methods and adaptive security actions (universal cloud storage). As technology developments and cyber dangers come to be extra innovative, companies are significantly focusing on anticipating analytics, expert system, and artificial intelligence to boost their information defense abilities in the cloud
Among the future trends in cloud data defense is the assimilation of automation and orchestration devices to streamline safety operations and response procedures. By automating routine jobs such as hazard discovery, event action, and patch management, organizations can improve their general security position and much better safeguard their information in the cloud.
Furthermore, the fostering of a zero-trust protection design is obtaining grip my blog in the realm of cloud data security. This strategy presumes that threats could be both external and interior, calling for constant authentication and permission for all customers and devices accessing the cloud setting. By applying a zero-trust framework, companies can minimize the risk of data violations and unapproved access to sensitive info kept in the cloud.
Final Thought
